The Salice Rose Nude Leaks: A Deep Dive Into Digital Privacy Violations And How To Protect Yourself
What really happens when private moments become public, and who is responsible when trust is shattered online?
The term "Salice Rose nude leaks" refers to the unauthorized distribution of private, intimate images allegedly involving the social media personality Salice Rose. This incident is not an isolated gossip story; it is a stark case study in the vulnerabilities of our digital age. It forces us to confront uncomfortable questions about consent, platform security, legal protections, and the human cost of cyber exploitation. This article will move beyond the sensational headlines to explore the factual timeline of the leaks, examine the broader epidemic of non-consensual image sharing, detail the legal avenues available to victims, and provide actionable strategies for fortifying your own digital privacy. Understanding this event is crucial for anyone who uses the internet, as it highlights risks that affect millions and empowers us to advocate for better safeguards.
Who is Salice Rose? A Brief Biography
To understand the impact of the leaks, it's important to know the person at the center of the storm. Salice Rose is a digital content creator and social media influencer who built a following primarily on platforms like Instagram and TikTok. Her content often features lifestyle vlogs, comedic sketches, and personal updates, cultivating a parasocial relationship with her audience. Like many influencers, her online persona is a blend of curated public life and moments of perceived authenticity, which makes the violation of her private life all the more jarring for her community.
| Personal Detail | Information |
|---|---|
| Full Name | Salice Rose (public persona) |
| Primary Platform | Instagram, TikTok, YouTube |
| Content Niche | Lifestyle, Comedy, Vlogging |
| Known For | Relatable daily content, engaging with fan community |
| Incident | Subject of non-consensual distribution of private images in 2023/2024 |
It is critical to note that the specifics of her personal life, beyond her public creator role, are her own. The focus must remain on the act of privacy violation, not on salacious details of the images themselves.
- Happy Anniversary Images Leaked The Shocking Truth Exposed
- Stuart Mad Tv Leak Secret Video Reveals His Darkest Secret
- Leaked Tianastummys Nude Video Exposes Shocking Secret
The Incident Unfolded: How Private Content Became Public
The "Salice Rose nude leaks" typically refer to the emergence of explicit photographs and videos on various online forums and social media platforms, purportedly showing her in private moments. These images were not shared by her; they were obtained and distributed without her consent, a act often termed "revenge porn" or non-consensual pornography. The content initially surfaced on lesser-known forums and image-sharing sites known for hosting such material, before being amplified across mainstream social media through accounts and pages that thrive on scandalous content.
The spread was rapid and algorithmic. Once posted, the images were saved, re-uploaded, and shared in private groups and public timelines. Hashtags and search terms related to her name were flooded, creating a digital wildfire that was difficult to contain. For Salice Rose, this meant a sudden, violent invasion of her privacy, transforming her from a content creator into a victim of a digital sex crime. The initial response from her team involved frantic takedown requests under the Digital Millennium Copyright Act (DMCA) and platform reporting policies, a reactive and often exhausting process against a constantly shifting tide of reposts.
The Pervasive Threat: Digital Privacy in the Social Media Age
This incident is a symptom of a much larger crisis. According to a 2023 report by the Cyber Civil Rights Initiative, over 1 in 4 women and 1 in 13 men have experienced the non-consensual sharing of their intimate images in their lifetime. The "Salice Rose nude leaks" scenario is a template repeated across thousands of cases annually. Our digital lives are built on a foundation of trust—trust in our devices, our apps, our cloud storage, and our partners. That trust is routinely exploited.
Why are we so vulnerable?
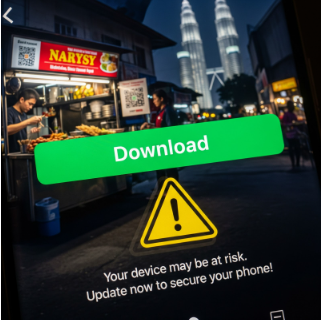
- Pervasive Data Collection: Every app we use, every cloud service we log into, creates potential access points. Weak passwords, unsecured Wi-Fi, and phishing scams can compromise accounts storing private photos.
- Intimate Partner Threat: A significant percentage of these leaks originate from a current or former intimate partner who had legitimate access to the images. This betrayal of trust is a common thread.
- The "Cloud" Illusion: Many people don't realize that photos backed up to services like iCloud or Google Photos can be accessed if an account is hacked or if security questions are guessed.
- Platform Design Flaws: Some platforms are slow to respond to reports or have cumbersome processes for victims to get content removed, allowing harm to compound.
Legal Frameworks and Victim's Rights: What Can Be Done?
The legal landscape is evolving but remains a patchwork. In the United States, 49 states plus Washington D.C. have laws against non-consensual image sharing, often called "revenge porn" laws. These laws typically make it a crime to distribute intimate images without consent, with penalties ranging from misdemeanors to felonies. Federal laws, like the Violence Against Women Act and the Computer Fraud and Abuse Act, can also apply, especially in cases involving hacking or interstate transmission.
Immediate Steps for a Victim (Actionable Guide):
- Document Everything: Take screenshots and URLs of every instance of the leaked content. Note dates, times, and platform names. This is crucial evidence for law enforcement and legal action.
- Report to Platforms: Use the dedicated reporting mechanisms on every site where the content appears. Report for violations of policies on "non-consensual intimate imagery" or "sexual exploitation." Be persistent.
- Contact Law Enforcement: File a report with your local police department. Provide all your documentation. Ask specifically about your state's non-consensual pornography law. You may also contact the FBI if the crime crossed state lines or involved hacking.
- Seek a Civil Harassment Restraining Order: Many states allow victims to seek court orders that legally prohibit the distributor from contacting them or posting further images, with criminal penalties for violation.
- Consult a Lawyer: An attorney specializing in cyber harassment or privacy law can advise on civil lawsuits for damages (emotional distress, invasion of privacy) and help navigate the complex takedown process.
The Invisible Wounds: Psychological and Social Impact
Beyond the legal and technical fallout, the psychological impact of such a leak is profound and often traumatic. Victims frequently report symptoms mirroring PTSD: anxiety, depression, hypervigilance, shame, and a loss of trust. The feeling of being permanently exposed online can lead to social withdrawal, damage to personal and professional relationships, and severe reputational harm. For public figures like Salice Rose, this is compounded by a public audience that may judge, victim-blame, or sensationalize their trauma.
- Loss of Autonomy: The core violation is the theft of one's narrative and bodily autonomy. The victim's most private self is weaponized for public consumption without their permission.
- Digital Footprint Permanence: Even if content is removed from major platforms, it can persist in cached pages, archives like the Wayback Machine, or private collections. This creates a perpetual fear of resurfacing.
- Professional Repercussions: Brands and collaborators may distance themselves due to perceived "controversy," leading to financial loss and career derailment, regardless of the victim's innocence.
Proactive Defense: Building Your Digital Fortress
While no one is ever to blame for having their privacy violated, there are proactive steps everyone can take to minimize risk. Think of this as digital hygiene.
- Audit Your Cloud: Regularly review what is stored in your iCloud, Google Photos, Dropbox, etc. Use strong, unique passwords and enable two-factor authentication (2FA) on every account that supports it.
- Device Security: Use passcodes, biometric locks (fingerprint/face ID), and keep your operating system and apps updated to patch security vulnerabilities.
- The "Would I Be Okay If This Was Public?" Rule: Before taking or sending an intimate photo, consider the worst-case scenario. If the answer is anything less than a resounding "yes," do not create or share the image. This is not about fear, but about informed consent.
- Secure Messaging: Use messaging apps with end-to-end encryption (like Signal or WhatsApp's private mode) for sensitive communications. Be aware that even these can be compromised if the device itself is lost or stolen.
- Educate Your Circle: Talk to partners and friends about digital consent. Make it clear that storing or sharing private images is a breach of trust and potentially illegal.
The Platform's Responsibility: Beyond Takedown Notices
Social media and content-sharing platforms bear significant responsibility. Their business models often rely on engagement, which can inadvertently promote the rapid spread of sensational, non-consensual content. While policies exist, enforcement is inconsistent.
- Proactive Detection: Platforms must invest in AI and human moderation to proactively identify and remove non-consensual intimate imagery before it goes viral, not just react to reports.
- Streamlined Reporting: The reporting process must be simplified, with clear categories for "non-consensual intimate imagery" and guaranteed faster response times.
- Preservation of Evidence: When content is removed, platforms should preserve the evidence (URLs, uploader info) for a reasonable period to assist law enforcement, without requiring a subpoena for the initial preservation.
- User Education: Platforms should prominently feature educational resources about digital consent and privacy settings within their apps.
Conclusion: Turning Violation into Vigilance
The "Salice Rose nude leaks" are a painful chapter in a larger story about the erosion of digital privacy. They remind us that behind every search term and viral post is a real person experiencing a profound violation. This event should not be consumed as mere celebrity scandal but understood as a critical societal issue. The path forward requires a multi-pronged approach: stronger, more uniform laws that empower victims and deter perpetrators; more responsible platform policies that prioritize safety over unchecked sharing; and widespread digital literacy that teaches consent and security as fundamental skills. For those who have experienced this violation, know that you are not to blame, and resources exist. For everyone else, let this be a catalyst for change. Advocate for better laws, demand accountability from tech companies, and most importantly, cultivate a digital culture that respects privacy as a fundamental human right, not a negotiable feature. The goal is not just to react to leaks like the one involving Salice Rose, but to build an online environment where such violations become exponentially harder to commit and easier to eradicate.