Boniface Gate Visitor Control Center: Your Complete Guide To Access, Security, And Efficiency
Have you ever wondered what happens behind the scenes at a major government or corporate facility the moment a visitor arrives? The answer almost always leads to a critical, often overlooked hub of operations: the Boniface Gate Visitor Control Center. This isn't just a simple check-in desk; it's the sophisticated nerve center responsible for managing the flow of people, ensuring uncompromising security, and facilitating seamless access to some of the most sensitive locations. Whether you're a first-time visitor feeling a bit nervous about the process, a facility manager benchmarking best practices, or simply curious about modern security infrastructure, understanding this center is key to appreciating modern access control. This comprehensive guide will demystify the Boniface Gate Visitor Control Center, exploring its pivotal role, the advanced technology that powers it, and why it represents the gold standard in secure visitor management.
The Strategic Importance of the Boniface Gate: More Than Just an Entrance
The Historical and Operational Significance of "Boniface Gate"
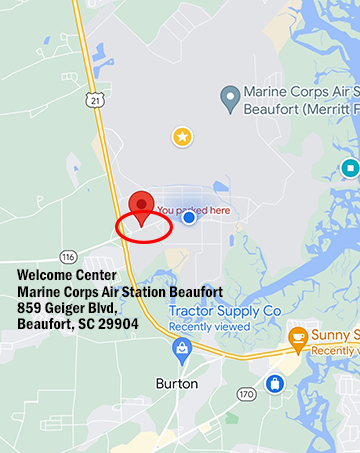
The name "Boniface Gate" itself often carries historical weight, potentially referencing a specific location, a former military installation, or a codename for a primary entry point to a high-security campus. Its significance lies in its function as the primary controlled access point. Unlike a public lobby, this gate is designed for controlled ingress, serving as the literal and figurative gateway between the outside world and a protected interior environment—be it a military base, a federal research facility, a major corporate headquarters with intellectual property, or a critical infrastructure site. The Visitor Control Center (VCC) positioned here is therefore not an afterthought but a foundational element of the site's security posture. Its location is deliberately chosen to allow for pre-screening before individuals reach any sensitive buildings or areas, creating a vital buffer zone.
Why a Dedicated Visitor Control Center is Non-Negotiable
In today's world, threats are diverse and sophisticated, ranging from physical intruders to insider threats. A dedicated VCC centralizes and standardizes the visitor intake process, eliminating ad-hoc, inconsistent procedures that create security gaps. It serves as the single point of accountability for visitor lifecycle management—from pre-arrival approval to on-site monitoring to departure logging. This centralization allows security personnel to maintain constant situational awareness. For instance, if an alert is triggered elsewhere on the campus, the VCC can instantly account for all visitors on the premises, a capability that is impossible with scattered check-ins. It transforms visitor management from a passive reception duty into an active, integrated security operations function.
Inside the Boniface Gate Visitor Control Center: A Step-by-Step Visitor Journey
The Pre-Arrival Phase: Setting the Stage for a Smooth Visit
The efficiency of the Boniface Gate VCC begins long before a visitor's car pulls up. Most modern centers utilize a digital pre-registration system. The host or sponsor within the secure facility initiates the process by submitting visitor details—full name, affiliation, purpose of visit, vehicle information, and sometimes even a photo—into a secure portal. This information is cross-referenced against watchlists and requires approval from the relevant security or administrative authority. The visitor then receives an email or SMS with a QR code or personalized check-in link, along with clear instructions on required identification (e.g., government-issued ID, passport), expected arrival time, and parking instructions. This phase drastically reduces wait times at the gate and allows the VCC team to prepare for the arrival, enhancing both security and visitor experience.
The On-Site Arrival and Screening Process: Technology Meets Human Vigilance
Upon arrival at the Boniface Gate, the process is methodical and multi-layered.
- Initial Approach & Document Verification: The visitor proceeds to a designated lane or kiosk. A VCC officer or an automated kiosk scans the pre-registration QR code. The officer then verifies the presented government ID against the pre-registered information. Biometric verification (like facial recognition or fingerprint scanning) may be employed for high-security sites, creating a digital "match" that is extremely difficult to spoof.
- Screening and Badge Issuance: After identity confirmation, the visitor and their belongings may undergo screening. This can range from a visual bag check to walk-through metal detectors and, in some cases, more advanced explosive trace detection (ETD) or millimeter-wave scanners for personnel. Once cleared, a temporary access credential—often a smart card, RFID badge, or even a disposable wristband—is issued. This badge is programmed with specific permissions: it may only work for certain doors, for a limited time (e.g., 4 hours), and will automatically deactivate upon departure or expiration.
- Escort and Accountability: For many facilities, visitors are not granted free movement. The system logs which sponsor or employee is responsible for the visitor. The sponsor is often required to meet the visitor at the VCC and remain with them throughout the visit, or the visitor is assigned to a designated escort. The VCC maintains a real-time electronic log of all visitors on-site, their locations (if tracked via badge or app), and their sponsors.
The Departure and Audit Trail: Closing the Loop
The visit concludes as rigorously as it began. Visitors are typically required to return their access badges to the VCC upon exit, either by dropping them in a slot or handing them to an officer. The system automatically logs the departure time. In cases where badges are not returned (e.g., lost), the system flags the credential as missing, triggering an alert to disable it and account for the individual. This creates a perfect audit trail. Every action—arrival, badge issuance, door access events, and departure—is timestamped and attributed. This data is invaluable for post-incident investigations, compliance reporting (for standards like ISO 27001 or NIST SP 800-171), and routine security audits. It answers the critical question: "Who was on our property, when, and where did they go?"
- Penny Barber
- Exclusive Leak The Yorkipoos Dark Secret That Breeders Dont Want You To Know
- The Nina Altuve Leak Thats Breaking The Internet Full Exposé
The Technological Engine: Systems That Power the Boniface Gate VCC
Integrated Visitor Management System (VMS) Software
The heart of the modern VCC is its Visitor Management System (VMS). This is not a simple sign-in sheet but a robust software platform that integrates multiple functions:
- Pre-registration & Invitation Management: Streamlines the sponsor-initiated process.
- Identity Verification: Interfaces with document scanners and biometric devices.
- Badge Production & Management: Controls credential printers and encodes access rights.
- Watchlist Screening: Often integrates with third-party databases (e.g., OFAC, terrorist watchlists) for automated checks.
- Real-time Dashboard & Reporting: Provides a live view of all visitors and generates compliance reports.
- eSignature Capture: For NDAs and legal agreements.
Hardware: The Physical Components of Security
The software relies on a suite of hardware:
- Document Scanners: High-resolution scanners that read ID barcodes, MRZs (Machine Readable Zones), and perform authenticity checks using UV/IR light.
- Biometric Readers: Facial recognition cameras or fingerprint scanners for identity proofing.
- Badge Printers: Instant issuance printers (often retransfer or card printer/encoder models) that produce durable, hard-to-forge credentials.
- Screening Equipment: Metal detectors, X-ray baggage scanners, and ETD units.
- Access Control Readers: The badges issued must be compatible with the facility's overall physical access control system (PACS).
- Kiosks & Terminals: Self-service options for pre-registered visitors to speed up the process.
Data Integration: The Key to Holistic Security
The true power of the Boniface Gate VCC lies in its system integrations. The VMS should not be a silo. It must communicate with:
- The Facility's Access Control System: To push badge permissions and log access events.
- Human Resources (HR) Systems: To automatically sync employee data for contractor or temporary worker visits.
- IT Systems (Active Directory/LDAP): For network access provisioning if visitors need temporary Wi-Fi or computer login.
- Video Management System (VMS/VMS): To associate a visitor's badge number with their video feed, allowing security to pull up footage of a specific individual instantly.
- Incident Management Platforms: To log any security incidents involving visitors directly into the central security log.
The Human Element: Staffing, Training, and Protocols
The Role of the VCC Officer
Technology is a tool, but the VCC officer is the critical decision-maker. Their role extends far beyond checking IDs. They are:
- Sentinels: Observant of behavior, demeanor, and potential deception.
- Customer Service Representatives: The first and last impression of the facility, needing to be professional, courteous, and clear in communication, especially with nervous or frustrated visitors.
- Procedural Experts: Must know all protocols inside out, from emergency evacuations to handling a "piggybacking" attempt (someone following an authorized person in).
- Problem Solvers: Handling issues like mismatched IDs, forgotten pre-registrations, or system outages with grace and adherence to security policy.
Essential Training and Certification
Effective VCC staff undergo rigorous, ongoing training covering:
- Access Control Policy: Deep understanding of the facility's specific security levels and requirements.
- Identification Skills: Advanced training in detecting fraudulent IDs and recognizing facial features for biometric matching.
- Screening Procedures: Proper and respectful use of screening equipment.
- Emergency Response: Protocols for fires, active threats, medical emergencies, and shelter-in-place orders, including how to account for all visitors during a crisis.
- Communication & De-escalation: Vital for managing difficult situations calmly.
- Legal and Compliance: Understanding privacy laws (like GDPR or CCPA if applicable) and data retention policies related to visitor information.
Emergency Response and Business Continuity: The VCC as a Command Post
The VCC's Role in Crisis Situations
During an emergency, the Boniface Gate VCC transforms from a visitor processing center into a critical command and control element. Its immediate actions are crucial:
- Cease All Visitor Ingress/Egress: The gate is locked down. No one enters or leaves without explicit, emergency-level authorization.
- Instant Accountability: Using its real-time electronic log, the VCC team can immediately provide first responders and incident commanders with a precise list of all non-employees on-site, their last known locations (from badge reads), and their sponsoring employees. This is invaluable for rescue operations and headcounts.
- Communication Hub: The VCC often has direct lines to the main security operations center (SOC), local law enforcement, and fire/EMS. It becomes the point of contact for coordinating the response regarding visitor-related matters.
- Evacuation Assistance: For planned evacuations, VCC staff can direct visitors to specific assembly points and assist in their safe accounting.
Business Continuity Planning
The VCC's procedures must be part of the facility's broader Business Continuity Plan (BCP). This includes:
- Redundant Systems: Backup power (UPS/generators) for all VCC technology.
- Alternate Processing Locations: A pre-identified secondary location (e.g., a nearby conference room) to process visitors if the primary VCC is compromised.
- Manual Procedures: Clear, practiced protocols for a complete technology failure, reverting to paper logs and manual badge issuance while maintaining security integrity.
- Regular Drills: Conducting joint drills with the facility's emergency response teams to test the VCC's role in a full-scale scenario.
Measuring Success: Metrics and Continuous Improvement
Key Performance Indicators (KPIs) for a Modern VCC
A well-run Boniface Gate VCC tracks several metrics to gauge effectiveness:
- Average Visitor Wait Time: The gold standard for visitor experience. Leading facilities aim for under 5 minutes for pre-registered visitors.
- First-Pass Clearance Rate: The percentage of visitors who complete the process without needing secondary screening or management intervention. A high rate indicates clear policies and good pre-screening.
- Incident Rate: Number and type of security incidents (e.g., attempted unauthorized entry, ID fraud detected) per month. A decreasing trend shows effective deterrence and detection.
- Compliance Audit Scores: Results from internal or external security audits specifically regarding visitor control procedures.
- Visitor & Host Satisfaction: Periodic surveys to gauge the experience from both sides.
The Cycle of Continuous Improvement
Data from these KPIs should feed into a cycle of review and improvement. For example, if wait times spike at 9:00 AM, the solution might be to stagger pre-scheduled appointments or add a temporary kiosk. If a certain type of ID is frequently flagged for potential fraud, staff training on that specific document's security features can be enhanced. The Boniface Gate VCC must be a dynamic system, adapting to new threats, technology updates, and operational feedback. Regular policy reviews, technology assessments, and tabletop exercises are essential to maintain a state of readiness.
The Broader Impact: Community, Compliance, and Culture
Beyond Security: Enhancing Reputation and Trust
A professional, efficient, and respectful visitor control center does more than stop bad actors; it enhances the reputation of the host organization. For a corporate client visiting a secure lab, a smooth, high-tech, and courteous check-in process reinforces an image of competence and innovation. For a government facility, it projects an image of order and seriousness. It builds trust with partners, contractors, and the public who have legitimate business on-site. Conversely, a chaotic, rude, or overly cumbersome process can sour relationships before the actual business meeting even begins.
Navigating the Compliance Landscape
The Boniface Gate VCC is a linchpin for meeting numerous regulatory and compliance obligations:
- Government Contracts (DFARS, ITAR): Strict visitor controls are mandatory for contractors handling Controlled Unclassified Information (CUI) or defense articles.
- Critical Infrastructure Protection (CIP): Standards from bodies like NERC for energy facilities mandate robust physical security, including visitor control.
- Data Privacy Regulations (GDPR, CCPA): The VMS must handle personal data (names, photos, ID numbers) lawfully, with clear retention policies and consent mechanisms where required.
- Industry-Specific Standards: ISO 27001 (Information Security), PCI DSS (for payment card data environments), and others all have requirements that a robust VCC helps satisfy.
Fostering a Security-Aware Culture
Finally, the VCC is a daily, visible reminder of the organization's commitment to security. It sets the tone for everyone who enters. A respectful but firm process teaches visitors that security is taken seriously. For employees, the requirement to sponsor and escort visitors reinforces their own responsibility in the security ecosystem. The Boniface Gate Visitor Control Center, therefore, is a cultural touchpoint, operationalizing the abstract concept of "security policy" into a concrete, shared experience that strengthens the overall security culture from the perimeter inward.
Conclusion: The Indispensable First Line of Defense
The Boniface Gate Visitor Control Center is far more than a checkpoint; it is a sophisticated, multi-layered system that stands as the indispensable first line of defense for any high-security facility. It masterfully blends advanced technology—from biometric scanners and integrated VMS software to seamless access control—with highly trained human judgment and rigorous protocols. Its operations span the entire visitor lifecycle, ensuring that every individual who crosses that threshold is known, verified, and accounted for, from the moment they arrive until the moment they depart.
In an era of complex threats, the difference between a secure and compromised facility often comes down to the integrity of its perimeter. The Boniface Gate VCC embodies that perimeter's intelligence and vigilance. It protects physical assets, intellectual property, and, most importantly, people. It ensures compliance, enables business continuity, and projects an image of unwavering professionalism. Whether you are planning to visit such a facility and want to know what to expect, or you are tasked with evaluating or designing a visitor control system, understanding the depth and breadth of this operation is crucial. The next time you pass through a controlled entrance, take a moment to appreciate the intricate dance of technology, procedure, and human expertise that makes secure access possible—that is the essence of the Boniface Gate Visitor Control Center.