Have You Been Ten-Printed? The Hidden Truth About Your Fingerprints In The Digital Age
Have you been ten-printed? It’s a question that rarely crosses the mind of the average person going about their day. Yet, the act of capturing all ten fingerprints—once a staple of police procedurals and spy thrillers—is now a routine part of accessing our phones, boarding planes, and even entering office buildings. The seamless convenience of touching a sensor to unlock your life is underpinned by a technology with profound implications for privacy, security, and personal identity. This comprehensive guide dives deep into the world of ten-printing, exploring its origins, its modern applications, the controversies it sparks, and what it truly means for you in an increasingly biometric world. Whether you’ve consciously enrolled your prints or not, understanding this technology is no longer optional—it’s essential.
What Exactly Is "Ten-Printing"? Beyond the Basics
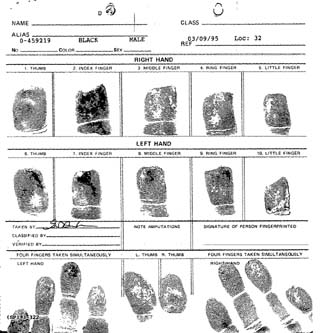
The term "ten-printing" originates from law enforcement and forensic science. In its strictest definition, it refers to the process of systematically capturing the rolled and flat impressions of all ten fingers onto a standard fingerprint card, like the FBI’s Form FD-258. Each finger is individually rolled from one side of the nail bed to the other to capture the full ridge detail, while the four fingers of each hand are pressed flat. This creates a comprehensive biometric record used for identification against vast criminal databases.
However, in the modern civilian context, "ten-printed" has evolved. It now colloquially describes any situation where an entity—a government agency, an employer, or a tech company—has collected and stored the biometric template derived from your fingerprints. This template is not a stored image of your print but a complex mathematical representation of its unique minutiae points (ridge endings, bifurcations). The shift from physical cards to digital templates is what has enabled the mass adoption of fingerprint technology in consumer electronics and beyond. The core principle remains: a unique, permanent physical characteristic is used as a key to verify "you."
- Driving Beyond Horizon
- Exposed Janine Lindemulders Hidden Sex Tape Leak What They Dont Want You To See
- Reagan Gomez Prestons Shocking Leak The Video That Destroyed Her Career
The Technical Journey: From Ink to Algorithm
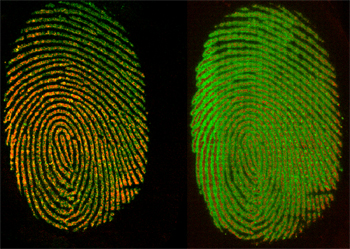
The journey of your fingerprint from your fingertip to a secure database is a marvel of miniaturization and computation. The old method involved ink, paper, and meticulous manual classification by experts. Today, optical, capacitive, or ultrasonic scanners capture the print. Optical scanners use light to create a visual image, capacitive scanners measure electrical charges to map ridges and valleys, and ultrasonic scanners use sound waves for a 3D map, which is harder to spoof.
Once captured, a sophisticated algorithm processes the raw data. It locates the core and delta points (the fingerprint's landmarks), extracts minutiae, and creates an encrypted template. This template is what’s stored and compared during future scans. The raw image is typically discarded, a critical privacy safeguard. The entire process, from placement to verification, now takes less than a second in a modern smartphone. This speed and reliability are why fingerprint authentication has become the world’s most widely deployed biometric modality.
A History Etched in Ridges: From Bertillon to Your Smartphone
The history of systematic fingerprinting is a fascinating tale of scientific breakthrough and institutional adoption. Before fingerprints, anthropometry (the Bertillon system) measured body parts. Its failure in a famous 1903 case led to the adoption of fingerprints in the UK and subsequently worldwide. Sir Francis Galton established the scientific basis for fingerprint uniqueness and permanence in the 1890s. The Henry Classification System, developed in India, allowed for efficient filing and searching of thousands of records.
- Geoff Tracy
- The Shocking Truth About Christopher Gavigan Leaked Documents Expose Everything
- Tennis Community Reels From Eugenie Bouchards Pornographic Video Scandal
For over a century, ten-printing was exclusively a domain of law enforcement and national security. The FBI’s Integrated Automated Fingerprint Identification System (IAFIS), launched in 1999, digitized decades of criminal records, creating a searchable database of over 70 million prints. This legacy infrastructure is the bedrock upon which modern civilian systems are often built or modeled. The pivotal shift to consumer use began with Microsoft’s Fingerprint Reader for Windows XP (2004) but truly exploded with Apple’s Touch ID in the iPhone 5s (2013). This move democratized biometrics, turning a tool of identification into a tool of convenience for billions.
The Pervasive Network: Where You’ve Been Ten-Printed (Often Without Realizing It)
You might think you’ve only ten-printed if you’ve been arrested or enrolled in Global Entry. The reality is far more expansive. Your fingerprints are likely stored in multiple databases, some of which you may have consented to without full awareness.
- Consumer Electronics: If you use Touch ID (iPhone/iPad/Mac), Face ID (which also uses a detailed facial map, a close cousin), or Android fingerprint sensors, you’ve enrolled your prints. Your biometric template is stored in a Secure Enclave—a hardware-isolated chip—theoretically never leaving your device. However, some apps request permission to use this authentication method, creating a chain of trust.
- Border Control & Travel: Programs like Global Entry (US), NEXUS (US/Canada), and eGates in the EU and Asia require fingerprint enrollment. These prints are cross-checked against watchlists (like the FBI’s NGI or Interpol databases) and stored in government travel databases for years.
- Employment & Workplace Access: Many corporations use fingerprint-based time clocks and door access systems. Your prints may be stored on a local server or a cloud-based security platform, often with policies that are less stringent than consumer devices.
- Financial Services: Some banks use fingerprint or voice recognition for phone banking authentication. While not a full ten-print, it’s still a biometric template.
- Schools and Universities: Increasingly used for lunch payments, library checkouts, and building access, capturing children’s biometrics from a young age.
- Rental & Sharing Services: Companies like Airbnb or car rental agencies are piloting fingerprint door locks, creating new data collection points.
The common thread is consent, often buried in terms of service, and a complex web of data storage practices with varying security levels.
The Double-Edged Sword: Convenience vs. Catastrophic Risk
The benefits are clear: unparalleled convenience and a stronger barrier against password theft. A fingerprint is something you are, not something you know or have, making it immune to phishing or keyloggers. However, the risks are uniquely severe because biometrics are permanent. You can change a compromised password; you cannot change your fingerprint.
- Irreversible Compromise: If a database containing your raw fingerprint images (not just templates) is breached, your biometric identity is forever exposed. Unlike a password, you can't "reset" your prints. Researchers have demonstrated methods to create fake fingerprints from high-resolution images or latent prints left on surfaces, a threat known as "spoofing."
- Function Creep and Surveillance: Data collected for one purpose—say, unlocking your phone—can be repurposed. Law enforcement has sought warrants to compel phone unlocking via fingerprint (a more legally contentious area than passcodes). There are fears of cross-database matching, where your workplace print could be checked against a criminal database without your knowledge.
- Accuracy and Bias Issues: No biometric system is 100% accurate. False Rejection Rates (FRR) and False Acceptance Rates (FAR) exist. Studies, including a landmark 2018 NIST report, have shown that some fingerprint algorithms exhibit racial and gender bias, with higher error rates for certain demographic groups, particularly those with worn prints from manual labor. This can lead to discriminatory outcomes in hiring or security checks.
- The "Boiling Frog" Effect: The gradual normalization of biometric collection lowers societal resistance. Each new app or office policy asking for a print feels like a minor trade-off for convenience, but the cumulative effect is a society where biometric surveillance becomes ambient and inescapable.
The Legal Landscape: A Patchwork of Protections
Globally, the law is scrambling to catch up with technology. There is no single, comprehensive international treaty on biometric data.
- The Gold Standard: GDPR (EU/UK): The General Data Protection Regulation classifies biometric data as a "special category" of personal data, requiring explicit, informed consent for processing. It grants individuals the right to erasure (the "right to be forgotten"), though this is legally complex for biometrics used for authentication. It also imposes heavy fines for breaches.
- The US Patchwork: There is no federal biometric privacy law. Instead, a state-by-state patchwork exists, led by Illinois' Biometric Information Privacy Act (BIPA). BIPA requires informed consent before collection, mandates a retention schedule, and allows for private right of action (lawsuits by individuals), leading to massive settlements against companies like Facebook and Google. Texas and Washington have similar laws, while California's CCPA/CPRA includes biometrics in its definition of personal information.
- Other Jurisdictions:China uses biometrics extensively for social control under its Social Credit System. The UK has a more surveillance-heavy approach under its Investigatory Powers Act. India's Aadhaar system, the world's largest biometric ID, has faced intense scrutiny over security and privacy.
The key takeaway: Your rights depend entirely on where you live and who is collecting your data. Always check the privacy policy, but know that these documents are often designed for legal compliance, not user clarity.
The Future is Biometric: What’s Next for Ten-Printing and Its Cousins
The trajectory points toward multimodal biometrics and continuous authentication. Relying on a single fingerprint is becoming seen as a single point of failure.
- Multimodal Fusion: Systems will combine fingerprint, facial recognition, voice patterns, and even behavioral biometrics (typing rhythm, gait) to create a probabilistic "identity score." Your phone might check your face as you pick it up and your fingerprint as you touch it, creating a more robust and spoof-resistant system.
- Behavioral Biometrics: This is the next frontier. Systems will passively authenticate you based on how you interact with devices—the pressure and swipe pattern on a touchscreen, your mouse movements, or even your unique heart rhythm (ECG) through a smartwatch sensor. This is continuous, invisible authentication.
- Decentralized Identity (SSI): A potential antidote to centralized database risks. Using blockchain-like technology, Self-Sovereign Identity would allow you to store your biometric template only on your personal device. When a service needs verification, your device would prove you match the template without ever sending the template itself. This is still nascent but holds promise.
- Regulatory Tightening: Expect more laws like BIPA to emerge globally, with a focus on data minimization (collect only what’s necessary), strict purpose limitation, and stronger individual control.
What This Means For You: A Practical Action Plan
Feeling overwhelmed? You’re not powerless. Here’s a concrete action plan to navigate the biometric landscape:
- Audit Your Digital Footprint: List every device, app, workplace, or program where you’ve enrolled a fingerprint or facial scan. Check settings for "Biometrics" or "Security."
- Demand Transparency: When asked to enroll, ask: Where is my biometric template stored? (On-device or cloud?)Who has access to it?What is the retention policy?Can I delete it? If the answer is vague, reconsider.
- Prioritize On-Device Storage: Favor systems like Apple's Secure Enclave or Android's Titan M2 chip, where the template never leaves your hardware. Be wary of systems that send biometric data to a central server for matching.
- Use Strong, Non-Biometric Fallbacks: Always set up a strong, unique passcode as an alternative authentication method. Do not rely solely on biometrics, especially for critical accounts like email or banking.
- Advocate for Policy Change: Support legislation like BIPA that provides strong, enforceable rights. Contact your representatives about the need for a federal biometric privacy standard in the US.
- Consider the Trade-Offs for Children: Be extremely cautious about enrolling a child’s biometrics in school or recreational programs. Their data is a lifelong identifier with no ability to consent meaningfully now.
- Stay Informed: Follow news about data breaches. If a service you use suffers a breach and they stored biometric data, treat it as a severe incident. Assume your template may be compromised and adjust your security posture accordingly.
Conclusion: Your Identity, Your Control
The question "have you been ten-printed?" is no longer just a query about a police procedure. It’s a fundamental question about your digital sovereignty. The fingerprints on your fingers are the keys to a new kingdom—one of effortless access but also unprecedented surveillance potential. The technology itself is neutral; its impact is shaped by the policies, laws, and corporate ethics surrounding it. As biometric authentication becomes as common as the password was, we must move from passive acceptance to active stewardship of our most permanent identifiers. The goal is not to reject this technology outright, but to demand its deployment with transparency, security by design, and robust legal guardrails. Your biometric identity is the last frontier of personal data. It’s time to understand who holds the keys.